Cybersecurity
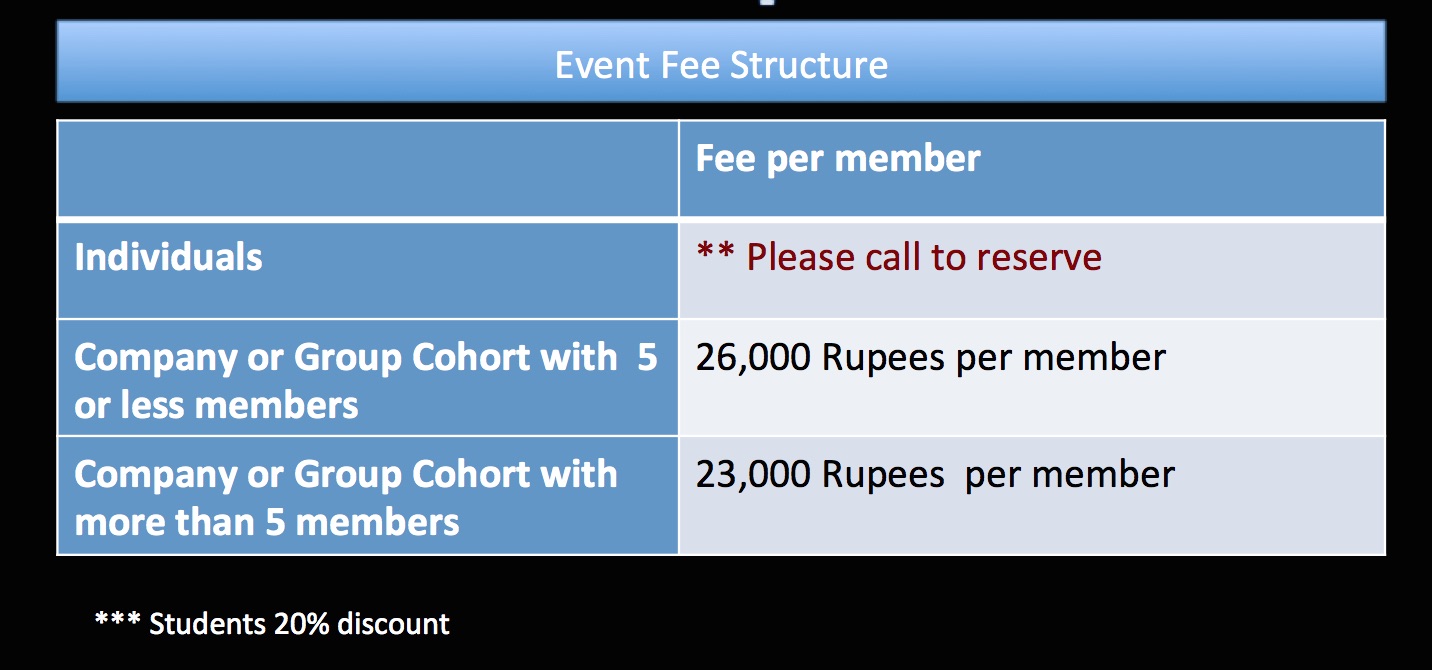
Fees: $2400
Duration: 10 Weeks
Days/Time: Lecture: Tuesday 7:00 pm - 9:30 pm
Cybersecurity
Email: Cyber Security
Phone (Hyderabad, India):
91 - 8179979892
Phone (USA):
(510) 791- 5759
(510) 209 - 6620
Phone (Hyderabad, India):
91 - 8179979892
Phone (USA):
(510) 791- 5759
(510) 209 - 6620
Program Plan

Real-time projects challenge the students’ learning and enable them to apply the class concepts to solve business requirements or industry problems. Here are some of the real-time mobile projects:
We've prepared exclusive interview pointers and questions bank for our registered students. You can access the questions bank using your student id and password.
Currently, our question bank can be accessed via HanuInnoTech Mobile App or On-line.

We've prepared exclusive interview pointers and questions bank for our registered students. You can access the questions bank using your student id and password.
Currently, our question bank can be accessed via HanuInnoTech Mobile App or On-line.
We've also published hard copy of question bank. Here is preview:
We've also published hard copy of question bank. Here is preview:
Week 1 (Getting Started)
Enterprise Software Overview
- Enterprise Software Technology Overview
- Client Server Architecture
- N-Tier to Cloud Models
Week 2 (Databases)
SQL Databases, Business Intelligence, Big Data Analytics
- NO SQL Databases, MongoDB, Indexed Databases, Cloud Databases
- Hadoop Databases, Map Reduce Processing
- Columnar Databases, Object Databases & Real- Time Processing, In Memory Databases
- Mobile Embedded Databases for iOS, Android, and Windows Phone
Week 3 (Client Server Transaction Transaction )
Client Server Transaction Transaction
- Message Queue & RPC Technologies
- Distributed Objects, The Web and Internet Technologies
- Java Objects, Distributed Systems management and Tools
- Service Oriented Architecture (SOA)
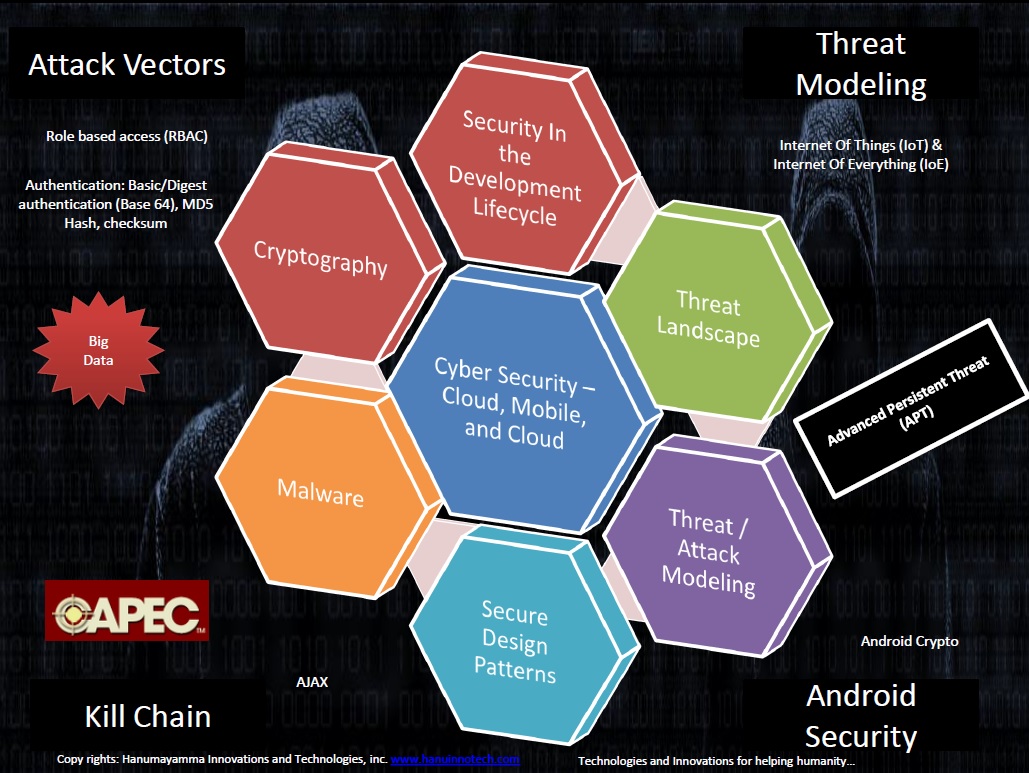
Week 4 (Security Framework Modeling)
Security Framework Modeling
- Authentication: Basic/Digest authentication (Base 64), MD5 Hash, checksum
- Confidentiality and Privacy: Symmetric or private-key, Asymmetric or public-key infrastructure (PKI), Digital signature, SSL
- Security Best Practices
- Java Sandbox Security Framework
- Mobile Devices Security Sandbox Models
<
Week 5 (Security Design Patterns)
Security Design Patterns
- Cloud Security & Mobile Security
- Java Crypto, Android Crypto, and iOS
- Malware detection - Web Frameworks
- Security Design Patterns
Week 6 (Mobile & Cloud Computing Common Threats)
Mobile & Cloud Computing Common Threats
Week 7 (Threat Modeling Tools)
Modeling Tools
- Data Flow Diagrams
- Asset Centric Modeing
- Attacker Centric Models
 Man In The Middle enables students to develop attack patterns that simulate MITM attack.
Man In The Middle enables students to develop attack patterns that simulate MITM attack.
 Data Encryption and Decryption services enable students to develop data protection services for data in transit and data in rest. Data Encryption Services can be consumed by Web and/or Mobile clients.
Data Encryption and Decryption services enable students to develop data protection services for data in transit and data in rest. Data Encryption Services can be consumed by Web and/or Mobile clients.
 Cloud SaaS / PaaS attack patterns enable students to develop Cloud Sercvice Provider (CSP) attack patterns & threat modeling .
Cloud SaaS / PaaS attack patterns enable students to develop Cloud Sercvice Provider (CSP) attack patterns & threat modeling .
 Mobile Monetization Threat Modeling enables students to develop services that identifies and mitigate security vulnerabilities on the Mobile platforms.
Mobile Monetization Threat Modeling enables students to develop services that identifies and mitigate security vulnerabilities on the Mobile platforms.